Sitecore hashes passwords for users and stores them in a database. Out of the box, Sitecore 9.1 and 9.1.1 use SHA1 as the hashing algorithm in the Web.config:
<membership defaultProvider=”sitecore” hashAlgorithmType=”SHA1″>
Unfortunately SHA1 is considered insecure (although it takes a bit of time and money to crack) so for safety it’s probably a good idea to change it to something stronger.
The algorithm can be changed to a number of different algorithms by changing the hashAlgorithmType in the Web.config file, but 9.1 introduced Sitecore Identity – a separate service running on Sitecore Host – which had a hardcoded dependency on SHA1 and did not allow it to be changed. There was also no config element that could be updated.
We lodged a ticket with Support and they provided a hotfix in response – 306226 – which enabled hashing with SHA1, SHA256, SHA384, SHA512, HMACSHA1, HMACSHA256, HMACSHA384, and HMACSHA512.
Below is a guide to installing the hotfix and updating Sitecore and Identity Server to use SHA512.
NOTE: Changing the hashing algorithm will prevent you from logging in and require that all current passwords are reset. Following the approach below should allow you to update your admin level password and not lock yourself out 😊
To change the algorithm:
- firstly log into the CM server as an admin level user,
- change the Web.config hashAlgorithmType from SHA1 to SHA512,
- refresh the Sitecore Dashboard screen,
- go to User Manager,
- change the password of the Admin user (or an admin level user of your choice),
- take a note of the new password.
This will ensure that you have a new SHA512 hashed password in the SQL database.
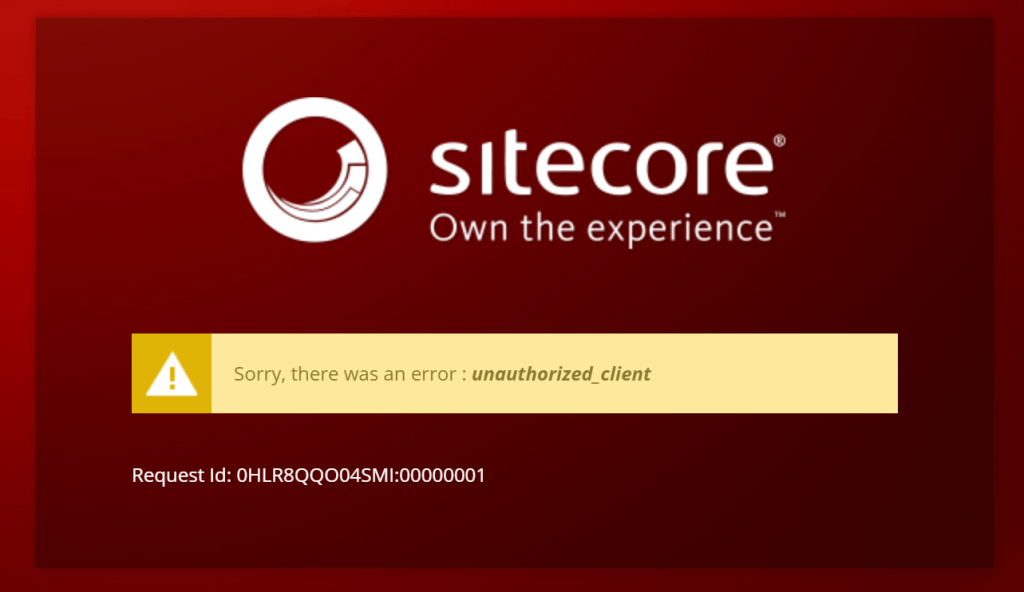
Now you can update the Identity Server with the hotfix and change it to SHA512.
To install the Hotfix:
- Stop the Sitecore Identity app service
- Copy the contents of the Website folder in the hotfix zip into the /site/wwwroot folder of the app service
- Edit the \sitecore\Sitecore.Plugin.IdentityServer\Config\identityServer.xml file and change the <PasswordHashAlgorithm> value
- Start the app service
You should now be able to log in to the CM server with the new password.
To revert, you can change back to SHA1 on the CM and SI roles and log in with a user that did not have their password changed.